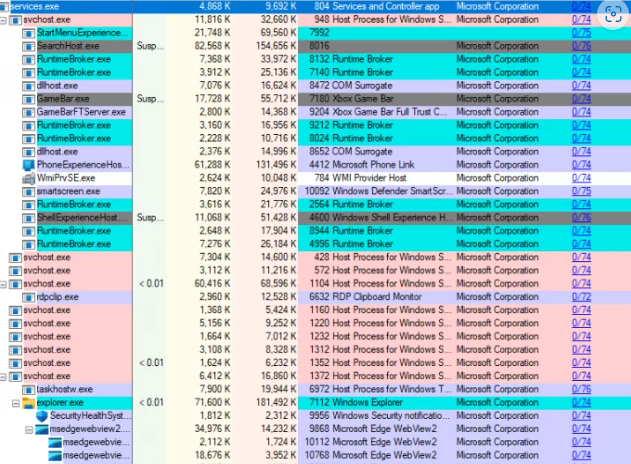
🔍How Process Explorer Enhances Cyber Security
Sysinternals Process Explorer is a powerful tool for I.T professionals to monitor and manage system processes, security, and performance. The software, free to download from
Sysinternals Process Explorer is a powerful tool for I.T professionals to monitor and manage system processes, security, and performance. The software, free to download from

Have you ever heard of the Air Gap Backups? This article discusses Air Gap Backups and how you can get the most out of them.

It’s a common theme. You begin seeing these amazing CGI images of your friends on Facebook or Instagram. You think, “How can I make one?”

Many small businesses make the mistake of skipping policies. They feel that things don’t need to be so formal. They’ll just tell staff what’s expected

Cloud file storage revolutionised the way we handle documents. No more having to email files back and forth. No more wondering which person in the

COMPTEC IT is proud to announce our latest and exciting partnership with The Innovative IT Solutions Provider, RetailCare. This newly formed partnership is the beginning

🔍 What’s Happening? ⚠ Attackers overwhelm users with spam emails, primarily newsletter sign-up confirmations from legitimate organisations.⚠ Follow-up phone calls from individuals impersonating IT team

From COMPTEC I.T , warm wishes for a bright and blessed Easter to you and your families!

💡 Our infographic highlights the key changes coming to Windows Server 2025, including new features and the removal of outdated functionalities. Here’s a quick rundown
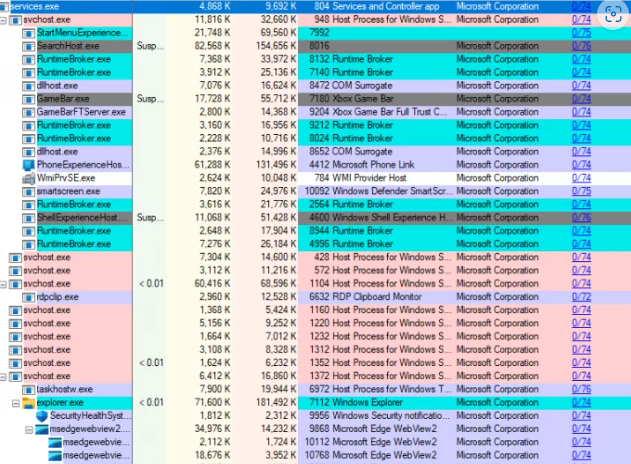
Have you ever seen a video of your favorite celebrity saying something outrageous? Then later, you find out it was completely fabricated? Or perhaps you’ve

QR codes are everywhere these days. You can find them on restaurant menus, flyers, and posters. They’re used both offline and online. QR codes are

Cloud computing has revolutionized the way businesses operate. It offers scalability, flexibility, and cost-efficiency. But cloud services also come with a downside: cloud waste. Cloud

In an era where digital transformation is not just an option but a necessity, Microsoft 365 has emerged as the cornerstone of corporate productivity, enabling
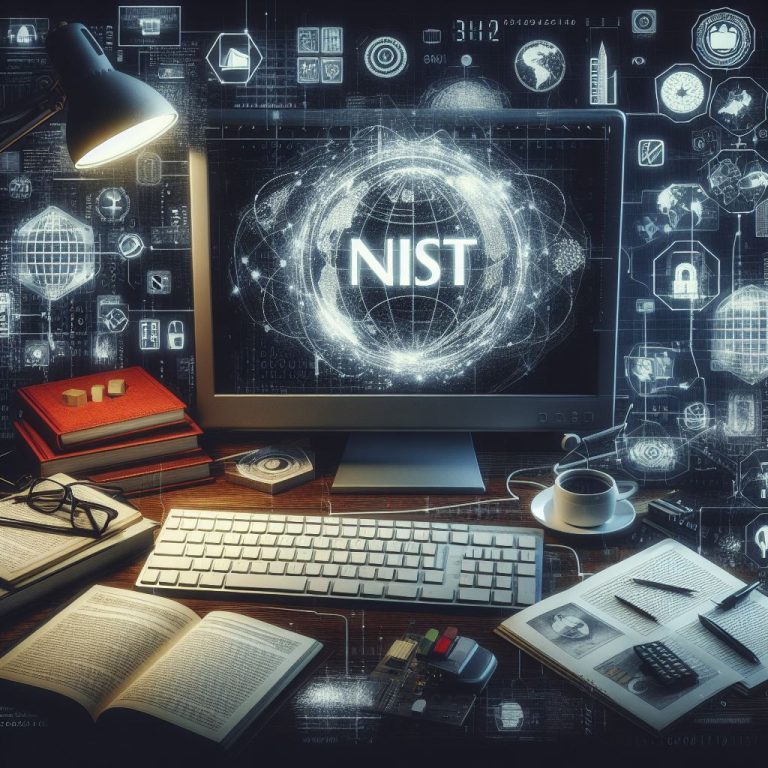
📢 #NIST Releases Version 2.0 of Landmark Cybersecurity Framework. This is the first major update since its creation 2014. The new edition is designed for all audiences,

Microsoft Edge continues to redefine user experiences. This is due to Microsoft’s commitment to innovation. The latest updates bring a host of features. These are
